Suspicious Local Admin Persistence
Executive Summary:
This lab simulates adding a domain user to the local administrator group and analyzes the generated Windows Security logs on the workstation. In a SOC context, this is classified as suspicious because it grants elevated privileges that persist across reboots and logouts. This lab demonstrates how unauthorized privilege escalation that deviates from normal user behavior can be identified through log analysis.
Lab Objective:
- Purposefully generated a local administrator group membership change on a workstation using an account with administrative privileges
- Observed Event ID 4732 to validate that the user was moved into the local Administrators group and identify the account responsible for the change.
- Exercise detection and analysis of unauthorized privilege escalation through log analysis.
Environment Overview
- Asset: Domain-joined Windows 11 workstation (Active Directory Environment)
- Log Source: Windows Security Event Log
- Tool: Event Viewer
Trigger / Simulated Activity
Simulated Action:A normal user account moved into the local Administrators group on a workstation.
Expected Signal:Event ID 4732 signaling a local group membership change, resulting in the user receiving administrative privileges.
Evidence Collected
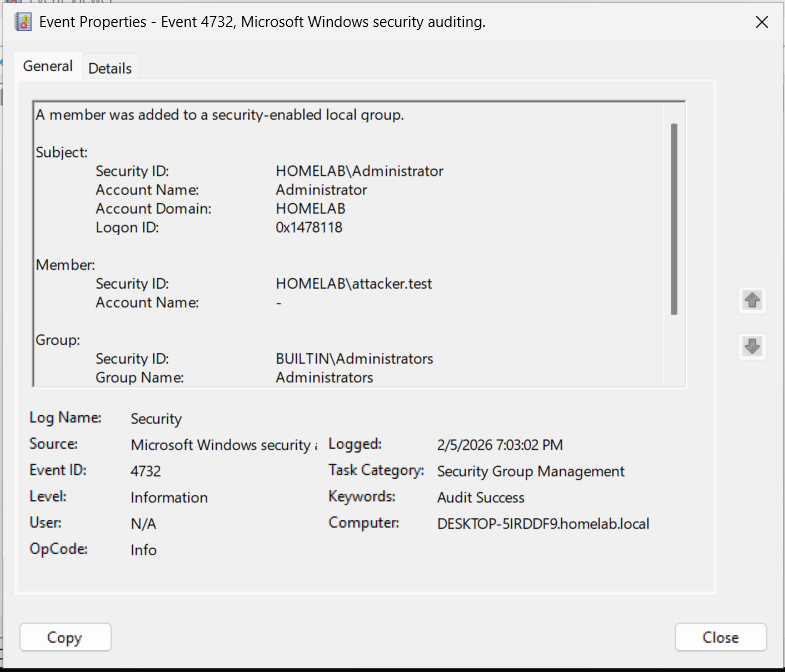
Log Artifacts:Primary Windows Security event confirming a change with a local Administrators group membership.
| Field | Value |
|---|---|
| Event ID | 4732 |
| Target Account | attacker.test |
| Actor Account | Administrator |
| Host | HOMELAB |
The screenshot shows Event ID 4732 confirming the user was added to the local Administrators group
 Supporting Evidence:
Supporting Evidence:
- Event ID 4672 indicates specialized privileges assigned to an administrative group.
- Event ID 4624 displays the Administrator account successfully logged in before the membership change
Analysis
Event ID 4732 verifies a local group membership change occurring on the workstation, where the account attacker.test was added to the local Admin group. The event assigns the action the account Administrator, indicating the change was performed utilizing admin privileges. This makes it unlikely that the action was performed independently by attacker.test.
The behavior observed aligns with expectations of the simulated activity. Moving a user to the local Administrators group results in the user receiving administrative rights that persist through logouts and shutdowns. This behavior is consistently reflected in the logs.
In a SOC environment, this activity would be triaged by confirming whether the change was an intentional and authorized action. The analyst would confirm the affected user was anticipated to have admin privileges and if the action is aligned with approved admin activity.
This analysis contains limitations and assumptions. Based on the available logs, it’s not possible to determine whether the administrator credentials were misused, whether the change was approved, or whether the action was performed locally or remotely.
Assessement
Severity:High
Confidence:Low
Rationale:- The account was moved from a normal user to an administrative user
- This user now has a persistent role as an admin user, which means this user has a broader range of system access
- It is unclear whether the account was moved intentionally or was authorized for this role
Detection Opportunities
- Observe Event ID 4732 for changes to the local Administrators group on the workstation
- Prioritize alerts where the target account is a non-administrative domain user
- During triage, validate whether the membership change was authorized by IT administrators.
SOC Analyst Takeaways
- Although the log shows the user was moved, the log alone cannot determine whether the action was authorized
- Verify the privilege changes with IT administrators during triage
Limitation
- The lab is limited to the workstation event log, which limits the ability to determine whether the activity represents a real threat
- Since the simulation was a lab, enterprise-wide scope and behavior are not represented
- Domain Controller logs were not available, reducing confidence in correlation
Conclusion
This lab has demonstrated detection of a normal user moved to local administrative group through local Windows Security logs. This is important because the log evidence alone must be verified with an IT administrator during triage.