Organizational Units & Group Policy Objects
Introduction
Organizational Units are basically folders inside your Active Directory domain, and Group Policy Objects are the rules you apply to those folders. OUs give structure to the domain by separating users and computers into logical groups. When everything is organized this way, admins can find users faster, troubleshoot issues more efficiently, and apply policies to entire groups instead of handling settings one person at a time.
For this lab, I’m keeping things straightforward. I’m creating a few Organizational Units, placing new users inside those units, and setting up a Group Policy to show how settings can be applied at the OU level. This builds on my last lab and walks through the first steps of organizing a domain and managing users or computers through Group Policy.
What Are Organizational Units (OUs)?
Organizational Units are basically folders inside your Active Directory environment that help keep everything organized. You’re placing users and computers into different groups, kind of like putting things into separate drawers so everything stays neat. In a real company, these groups are usually named after departments.
Setting things up this way makes admin work a lot easier. You can find users faster, and you can apply one policy to an entire department by targeting a single OU instead of changing settings for every person individually. Cybersecurity teams also depend on OUs because they help reduce the attack surface, enforce stricter settings, and monitor anything that looks suspicious.
Creating an Organizational Unit
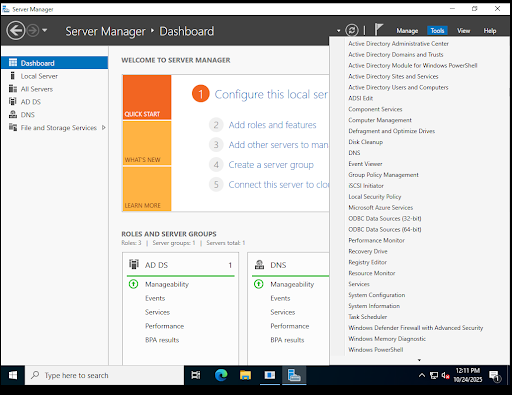
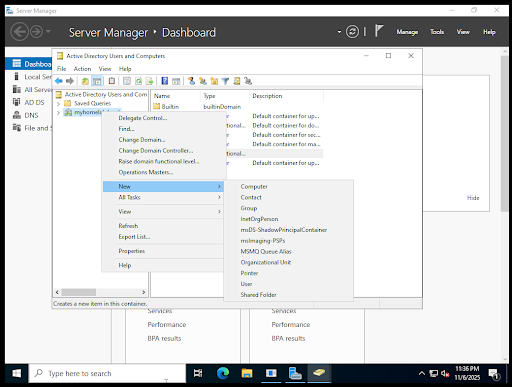
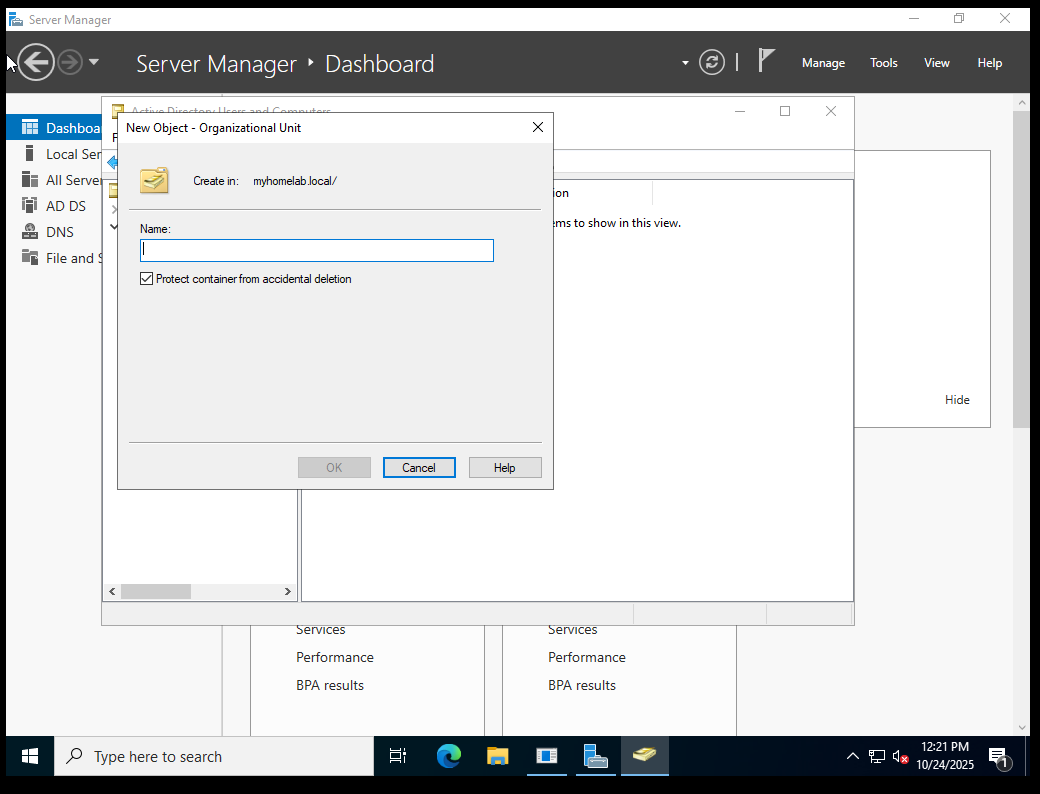
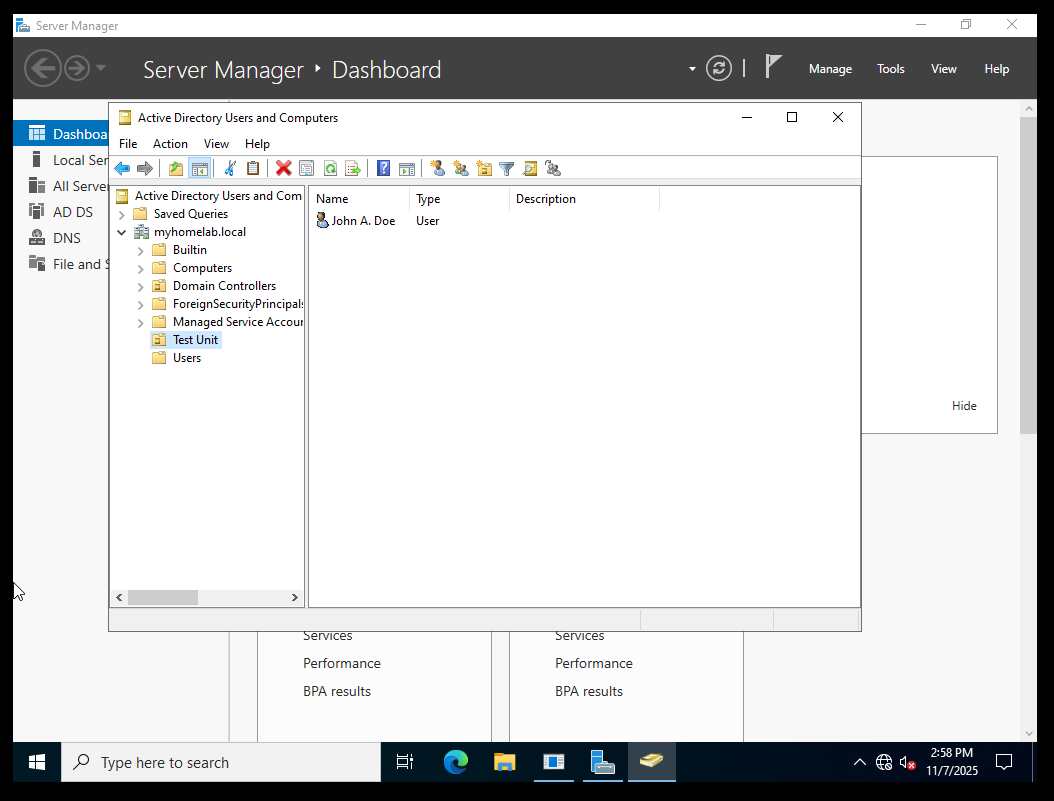
In Active Directory Users and Computers, I right-clicked my domain and selected New > Organizational Unit. You can access Active Directory Users and Computers through Tools at the top right of Server Manager.
I named mine Test Unit, but normally it would be named after the department it’s meant to manage.
Adding Users Inside an OU
It’s really important to keep users in the OU that matches their actual department. Doing this makes everything easier—finding users, applying policies, reducing mistakes—and overall, it leads to better security.
I went ahead and added a user by right-clicking the OU and selecting New > User. That opens the wizard for creating a new user. From there, just fill in the user’s details, set the initial password, and decide whether you want to let the user change it or not.
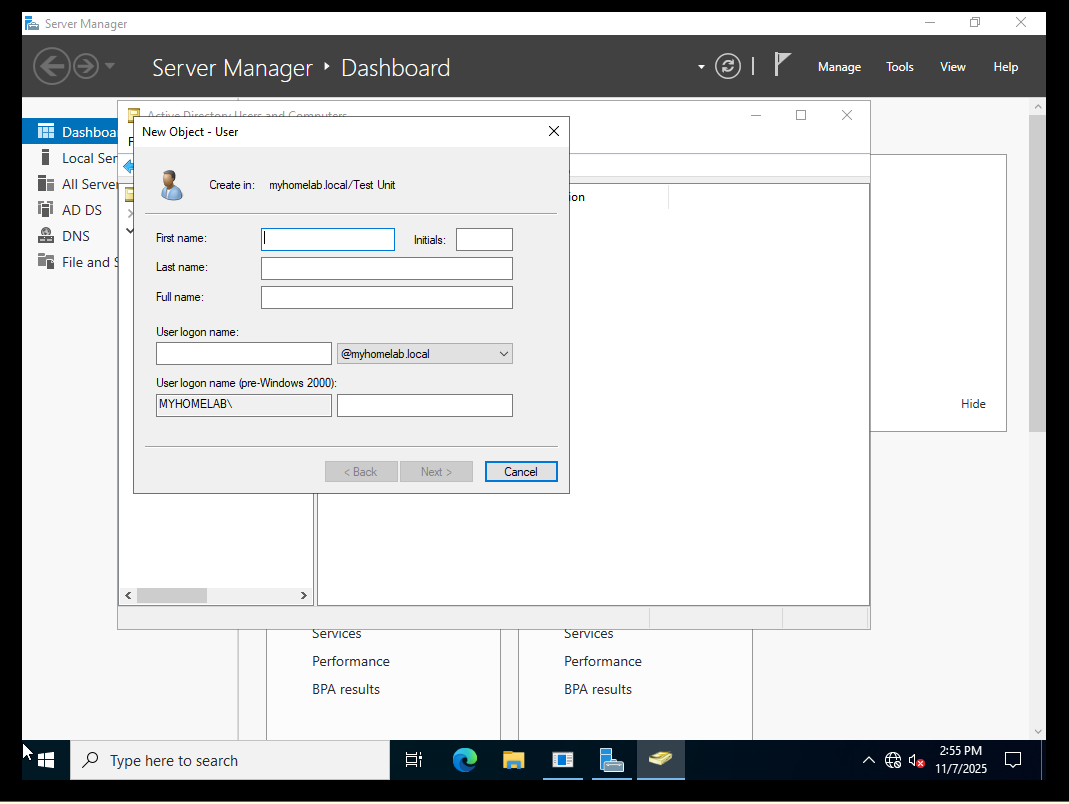
Most companies follow a naming pattern to keep account names predictable. Some common examples are j.doe, john.doe, or it-jdoe. The point is to pick a format and stick with it so every login stays consistent.
Once your users are in the correct OUs, admin tasks become a lot easier to manage, and you avoid unnecessary downtime.
Creating and Linking a Group Policy
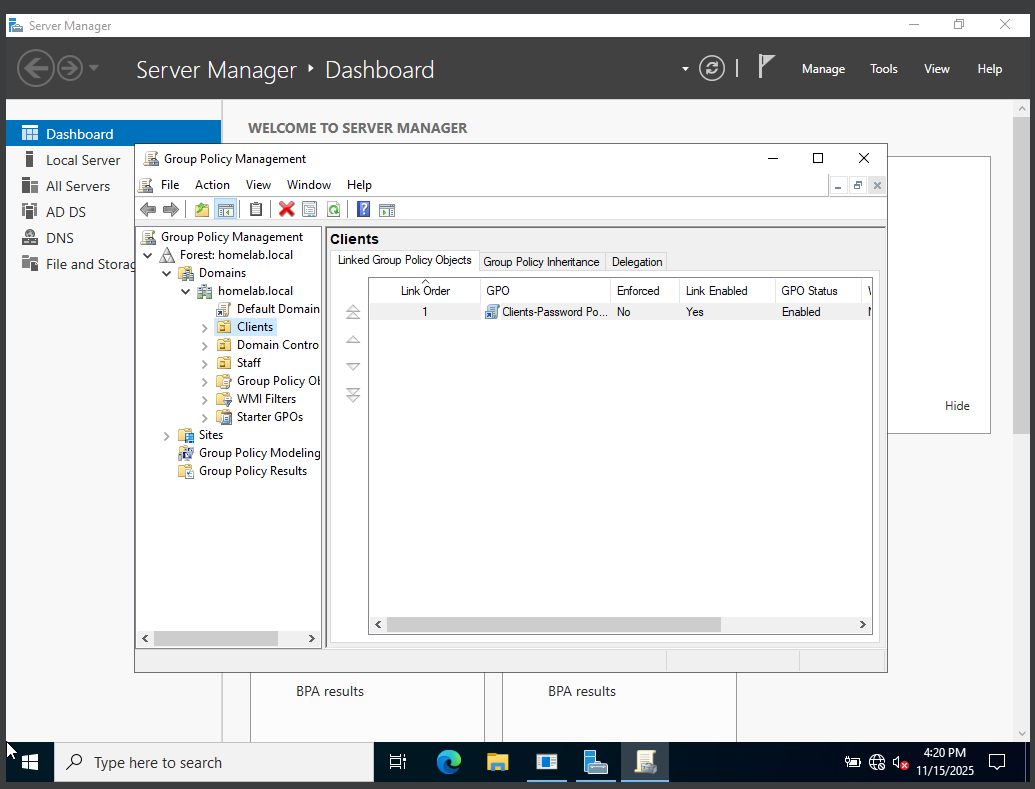
A Group Policy Object is what you use to apply rules to a set of users or computers. The GPO is basically a book of rules that gets applied to whatever OU it’s linked to. To do that, you need to access the Group Policy Management Console. Here are the steps:
- Click Tools in the top-right corner.
- Select Group Policy Management.
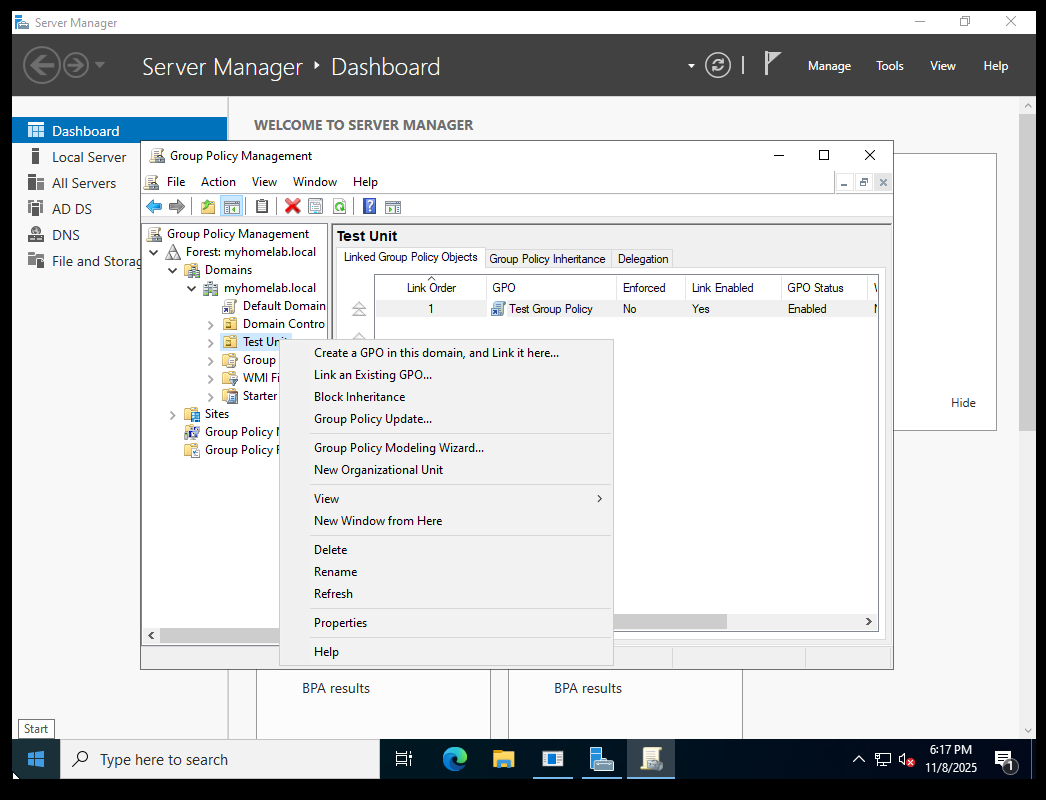
Next, expand your domain. Right-click the OU and select Create a GPO in this domain, and Link it here…
When naming GPOs, it’s best to use a name that clearly explains what the policy does. This makes it easy to identify without having to dig through the settings later. If you already have a GPO created and just want to link it, choose Link an Existing GPO instead.
Linking a GPO to the correct OU is extremely important for staying organized. You don’t want the wrong group of users or computers to be restricted by policies that don’t apply to them. Keeping GPOs tied to the right OUs prevents confusion because you always know who the policy affects, why it’s applied, and what OU it’s connected to. It also helps ensure users only have the access they actually need—nothing more.
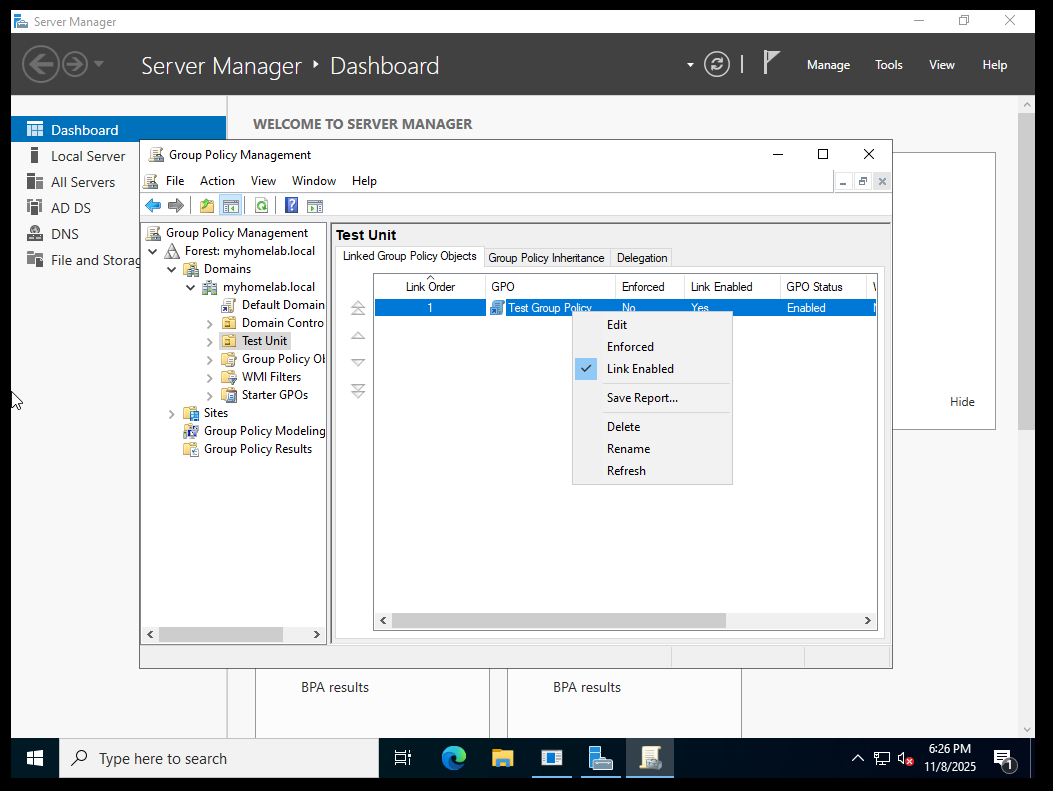
Editing Group Policy Settings
Here’s where we get to the part where the Group Policy settings are edited. To do this, you need to right-click the GPO and select Edit. I then navigated to the password policies by going to:
Computer Configuration > Policies > Windows Settings > Security Settings > Account Policies > Password Policy
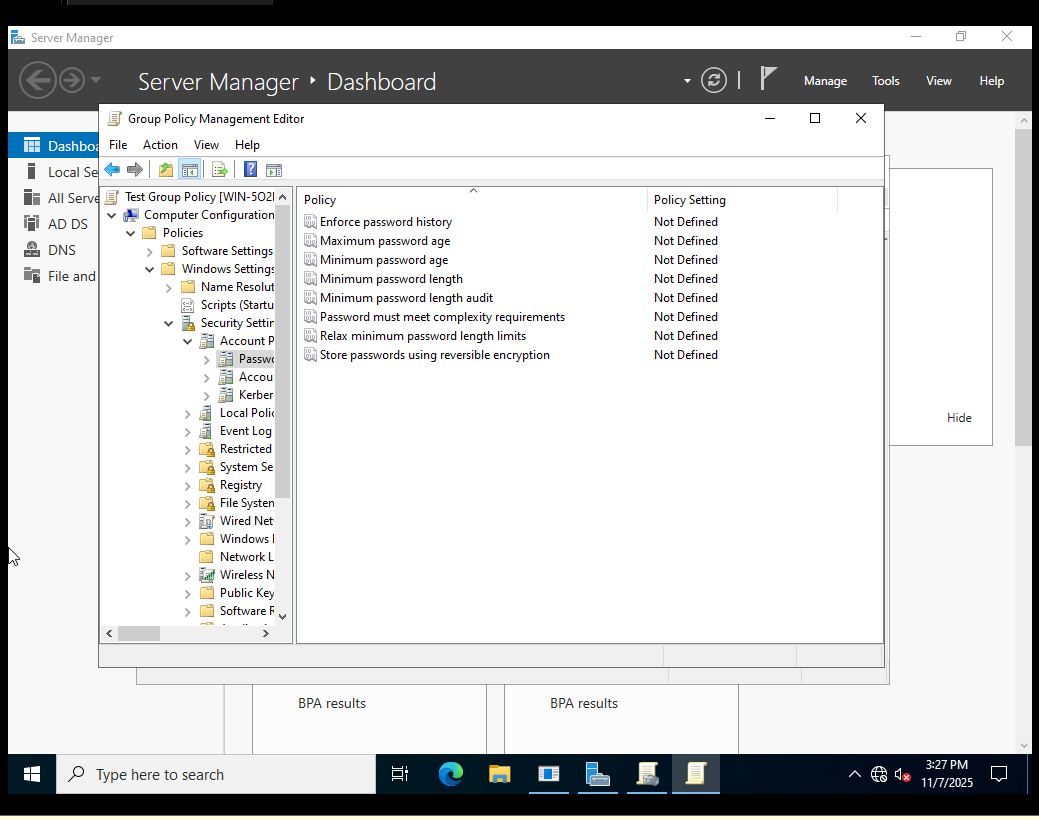

Here, you can see the password policies you can enforce on users.
Why OUs + GPOs Matter in Security
It’s very important that role-based access controls are applied, since you only want users to have access to what they actually need. Roles must be locked down to prevent widespread damage if an account is ever compromised. You want walls in place to keep any malware or suspicious activity isolated instead of spreading across the domain.
As mentioned before, troubleshooting is much faster when users are organized into OUs. Instead of searching through hundreds of accounts, you can go straight to the group that user belongs to and find them immediately. And with the structure provided by GPOs and OUs, auditing becomes much easier. It also shows auditors that you’re following a proper security framework.
Instead of accidentally applying the wrong policy to the entire domain, a mistake would only affect a single OU. OUs protect you by isolating the blast radius. Mistakes happen—so containment is extremely important.
Final Thoughts
In this lab, I set up a basic Active Directory structure using OUs and GPOs. I built a clean layout where users were placed inside the correct OUs and walked through where the policy settings are located so they can be assigned to the right groups. This kind of structure keeps the environment organized and creates a solid foundation for future labs.
It sets the stage for things like log collection, privileged access management, SIEM integration, and any other security-focused work you plan to build on top of your domain.
Understanding how OUs and GPOs work is extremely important for any security analyst working in a Windows environment. These controls help contain damage, enforce access boundaries, and make administration and investigations much easier. They also reduce the chances of major mistakes—like applying a restrictive policy to the entire domain instead of a single department.
Even if you’re not a domain administrator, knowing how OUs and GPOs function makes you better at spotting issues when they show up. It helps you understand how attackers move through the network, which paths they’re likely to take, and what they might try to exploit. With that knowledge, you’re able to respond to incidents more confidently and recognize misconfigurations or suspicious behavior before it becomes something bigger.